10 Types of E-Commerce Fraud & How to Prevent Them

Table of Contents
E-commerce has revolutionized the way we shop and conduct business, offering convenience and accessibility like never before. However, with the rise of online transactions comes the looming threat of e-commerce fraud. Understanding the various types of e-commerce fraud, the businesses most at risk, current trends, and future predictions is crucial for safeguarding both consumers and companies in the digital marketplace. In this article, we’ll explore the ins and outs of e-commerce fraud, including its definition, types, impact on different businesses, emerging trends, and most importantly, prevention techniques.
What is e-commerce fraud?
E-commerce fraud refers to any fraudulent or illegal activity conducted during an online transaction. This can include unauthorized access to sensitive information such as credit card details, identity theft, phishing scams, chargeback fraud, and more. Essentially, any deceptive practice aimed at exploiting vulnerabilities in the online payment process constitutes e-commerce fraud.
Types of e-commerce fraud
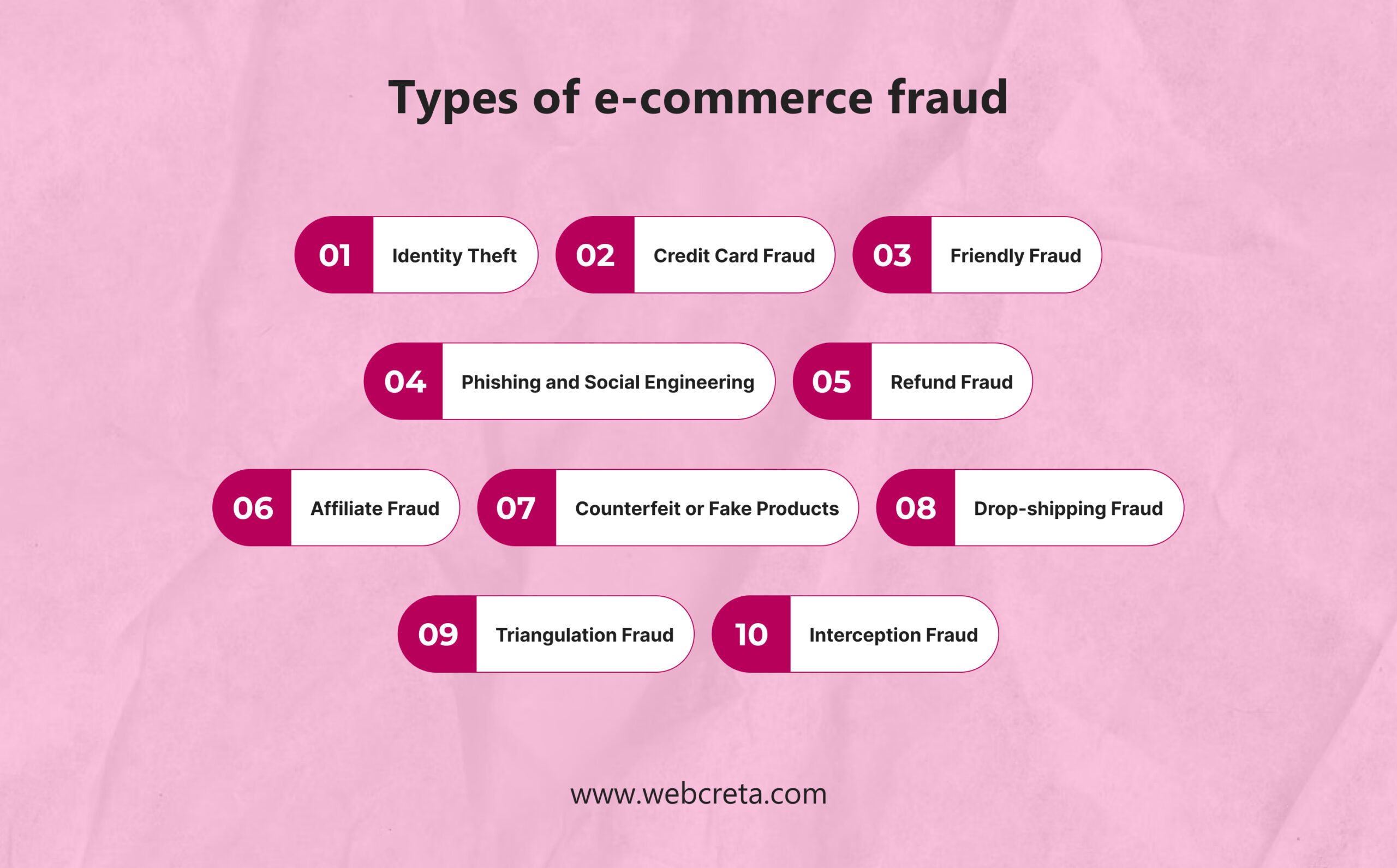
A) Identity Theft:
- This form of e-commerce fraud involves the unauthorized use of personal information, such as name, address, social security number, or credit card details, for fraudulent activities.
- Cybercriminals typically acquire this information through various means, including data breaches, phishing scams, or malware attacks. Once obtained, they can use the stolen identity to make purchases, open accounts, or conduct other fraudulent transactions without the victim’s knowledge.
B) Credit Card Fraud:
- Credit card fraud occurs when criminals use stolen or counterfeit credit card information to make unauthorized purchases online.
- This type of fraud can take various forms, including card-not-present transactions, where the cardholder’s physical presence is not required. Fraudsters may obtain credit card information through data breaches, skimming devices, or phishing scams.
C) Friendly Fraud:
- Chargeback fraud, also known as friendly fraud, involves customers disputing legitimate transactions with their credit card issuer to fraudulently obtain refunds.
- This can occur when a customer falsely claims that they did not receive the purchased goods or that the transaction was unauthorized.
D) Phishing and Social Engineering:
- Phishing involves the use of deceptive emails, websites, or messages to trick individuals into divulging sensitive information, such as login credentials or financial data.
- Social engineering tactics manipulate human psychology to exploit trust or fear, often leading individuals to disclose confidential information willingly.
- Phishing and social engineering attacks are commonly used by cybercriminals to obtain personal and financial information for fraudulent purposes.
E) Refund Fraud:
- Refund fraud occurs when individuals exploit the return and refund policies of online retailers to obtain undeserved refunds or replacements.
- This can involve returning counterfeit or used items, exploiting loopholes in the refund process, or falsifying return requests to deceive merchants into issuing refunds improperly.
F) Affiliate Fraud:
- Affiliate fraud involves manipulating or exploiting affiliate marketing programs to generate fraudulent commissions or revenue.
- This can include using fake or stolen identities to sign up as affiliates, engaging in click fraud to artificially inflate referral traffic or sales, or colluding with others to manipulate tracking systems and claim undeserved commissions.
G) Counterfeit or Fake Products:
- Counterfeit or fake products refer to goods that are unlawfully replicated or imitated to deceive consumers into believing they are purchasing genuine items.
- Counterfeit products are often sold through unauthorized online marketplaces or websites, posing significant risks to consumers in terms of quality, safety, and legality.
H) Drop-shipping Fraud:
- Drop-shipping fraud occurs when fraudulent sellers exploit the drop-shipping model to deceive buyers and evade accountability.
- This can involve advertising products at unrealistically low prices, failing to deliver purchased items, or misrepresenting product quality or specifications to unsuspecting customers.
I) Triangulation Fraud:
- Triangulation fraud involves a complex scheme where fraudsters use intermediaries to facilitate fraudulent transactions while concealing their identity and location.
- In this scheme, the fraudster typically poses as a legitimate seller, while an unwitting third party, often a compromised account or individual, is used to receive payments or forward purchased items to the fraudster.
J) Interception Fraud:
- Interception fraud, also known as man-in-the-middle attacks, occurs when cybercriminals intercept communication between buyers and sellers during online transactions to manipulate or divert payments.
- This can involve compromising the security of e-commerce platforms, intercepting sensitive information, such as payment details or login credentials, and redirecting funds to fraudulent accounts.
Which Types of Business Sectors Facing E-commerce Fraud Challenges?

A) Online Retailers:
E-commerce platforms and online retailers, especially those dealing with high transaction volumes, are prime targets for various forms of fraud, including credit card fraud, identity theft, and counterfeit product scams.
B) Digital Service Providers:
Businesses offering digital services such as software subscriptions, streaming platforms, or online courses are vulnerable to subscription fraud, where fraudsters use stolen payment information to access services without authorization.
C) Marketplace Platforms:
Online marketplace platforms connecting buyers and sellers face risks related to fraudulent transactions, counterfeit product listings, and seller impersonation scams, as they facilitate a large volume of transactions and interactions between parties.
D) Financial Institutions:
Banks, payment processors, and other financial institutions involved in processing online transactions are susceptible to fraud-related risks, including credit card fraud, chargeback fraud, and money laundering activities.
E) Travel and Hospitality:
Businesses in the travel and hospitality sector, including airlines, hotels, and booking platforms, are targets for various forms of fraud, such as identity theft, booking scams, and fraudulent chargebacks related to canceled or disputed reservations.
F) Small and Medium-sized Enterprises (SMEs):
SMEs may be more vulnerable to e-commerce fraud due to limited resources for implementing robust fraud prevention measures, making them attractive targets for fraudsters seeking to exploit weaknesses in their systems and processes.
The Changing Landscape of E-commerce Fraud: Trends and Forecasts
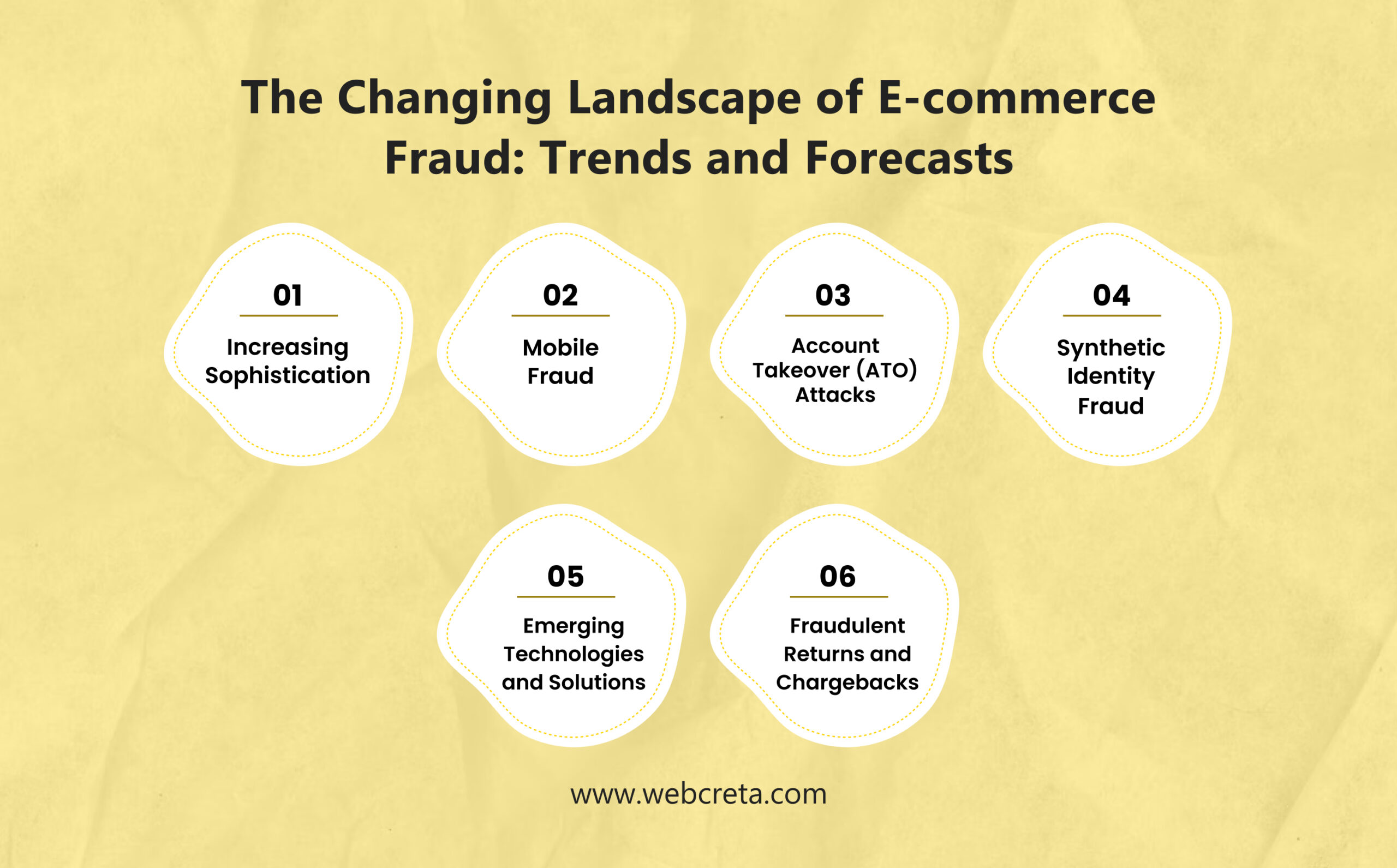
A) Increasing Sophistication:
E-commerce fraudsters are continually evolving their tactics and techniques, leveraging advanced technologies such as artificial intelligence (AI) and automation to carry out more sophisticated attacks. As fraud prevention measures improve, fraudsters adapt their strategies to circumvent detection and exploit vulnerabilities in online systems.
B) Mobile Fraud:
With the growing popularity of mobile commerce (m-commerce), fraudsters are increasingly targeting mobile devices for fraudulent activities, including mobile app fraud, SMS phishing (smishing), and mobile payment fraud. As mobile usage continues to rise, mobile-specific fraud prevention measures will become increasingly important.
C) Account Takeover (ATO) Attacks:
Account takeover attacks, where fraudsters gain unauthorized access to user accounts by stealing login credentials or exploiting security vulnerabilities, are on the rise. ATO attacks enable fraudsters to carry out various fraudulent activities, including making unauthorized purchases, accessing sensitive information, and perpetrating identity theft.
D) Synthetic Identity Fraud:
Synthetic identity fraud involves creating fictitious identities using a combination of real and fabricated information to open fraudulent accounts or obtain credit. This type of fraud is challenging to detect, as fraudsters use a blend of legitimate and fabricated data to create synthetic identities that may go undetected by traditional verification methods.
E) Emerging Technologies and Solutions:
Advances in technology, such as machine learning, biometrics, blockchain, and behavioral analytics, are enabling businesses to develop more advanced and effective fraud prevention solutions. These technologies offer new opportunities for detecting and preventing fraud in real-time, enhancing security, and improving the overall customer experience in e-commerce.
F) Fraudulent Returns and Chargebacks:
Fraudulent returns and chargebacks, where customers exploit return policies or dispute legitimate transactions to obtain refunds fraudulently, are a growing concern for online retailers. Fraudulent returns and chargebacks can result in financial losses, increased operational costs, and damage to merchant reputation.
E-commerce fraud prevention and detection Techniques
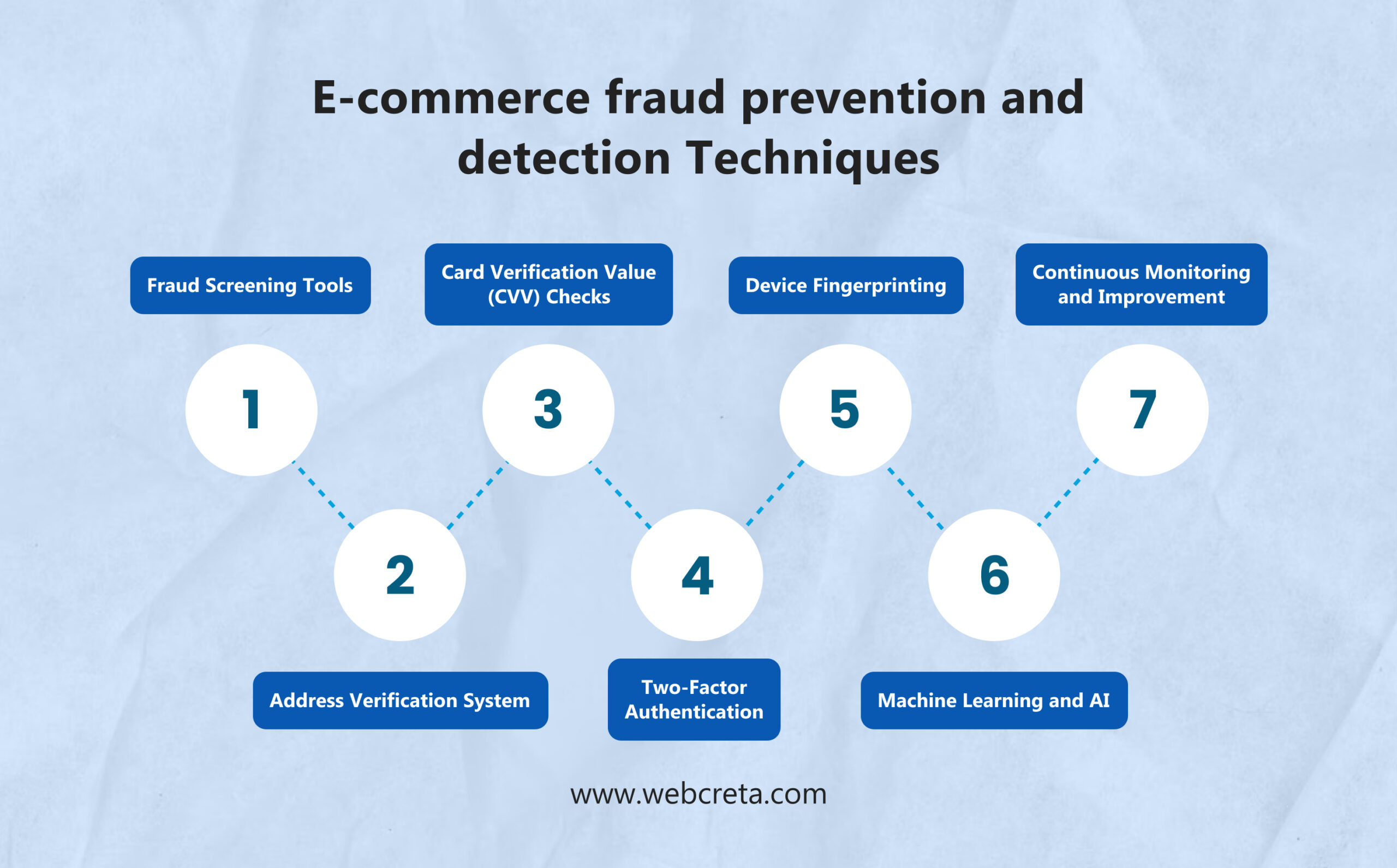
A) Fraud Screening Tools:
Implement fraud screening tools and services that analyze transaction data in real-time to identify suspicious activities, such as unusual purchase patterns, high-risk IP addresses, or suspicious behavior during checkout. These tools can help merchants flag potentially fraudulent transactions for further review or verification.
B) Address Verification System (AVS):
Utilize AVS to verify the billing address provided by the customer during checkout against the address on file with the credit card issuer. AVS helps detect discrepancies between the billing address and the cardholder’s address, reducing the risk of fraud associated with unauthorized transactions.
C) Card Verification Value (CVV) Checks:
Require customers to provide the CVV code printed on the back of their credit card during online transactions. CVV checks help verify that the customer has physical possession of the card, adding an extra layer of security to the payment process and reducing the risk of card-not-present fraud.
D) Two-Factor Authentication (2FA):
Implement 2FA mechanisms, such as SMS verification codes, email verification links, or biometric authentication, to verify the identity of customers during login or checkout. 2FA adds an extra layer of security by requiring customers to provide a second form of authentication, reducing the risk of account takeover and unauthorized access.
E) Device Fingerprinting:
Utilize device fingerprinting techniques to analyze unique characteristics of customers’ devices, such as IP address, browser type, and device ID, to detect suspicious or fraudulent activities across multiple transactions. Device fingerprinting helps identify and block fraudsters using the same device for fraudulent transactions.
F) Machine Learning and AI:
Leverage machine learning and artificial intelligence algorithms to analyze vast amounts of transaction data and identify patterns indicative of fraudulent behavior. Machine learning models can learn from historical data to detect emerging fraud trends and adapt to evolving fraud tactics in real-time, improving the accuracy of fraud detection and reducing false positives.
G) Continuous Monitoring and Improvement:
Implement a continuous monitoring and improvement process to evaluate the effectiveness of your fraud prevention measures, identify areas of weakness or vulnerability, and implement enhancements or updates as needed. Regularly review transaction data, fraud trends, and performance metrics to refine your fraud prevention strategy and stay ahead of evolving fraud threats.
Discover how Webcreta collaborates with businesses to proactively prevent e-commerce fraud and swiftly detect and respond to any suspicious activity. Learn more now!